Identity and access management (IAM) refers to a set of technologies and processes that manage and secure digital identities and access to resources, systems, and data within an organization. The resources mentioned include access to applications, networks, infrastructure, and data. Moreover, IAM is based on the premise of building trust in the digital ecosystem. In simpler terms, IAM is a framework of policies and technologies that primarily aims to protect your organization from external and internal threats.
These solutions help organizations to establish and maintain the identity of their employees, customers, partners, and other stakeholders, and to control their access to digital resources and applications based on the user’s identity, role, and context.
Let us delve deeper into how Identity and Access Management works and how it supports compliance with regulatory requirements for information security.
How do Identity and Access Management Work?
The core components of IAM include identity provisioning, authentication, authorization, and access management. Identity provisioning is the process of creating, modifying, and disabling user accounts and access privileges. Authentication verifies the identity of users while authorization controls what actions a user can perform once they are authenticated. Lastly, access management governs how users access and use resources and applications within the organization. With all these factors working in coordination, Identity and Access Management systems are used as the sole directory to create, modify, and delete users.
The basic steps involved in how Identity and Access Management works are:
-
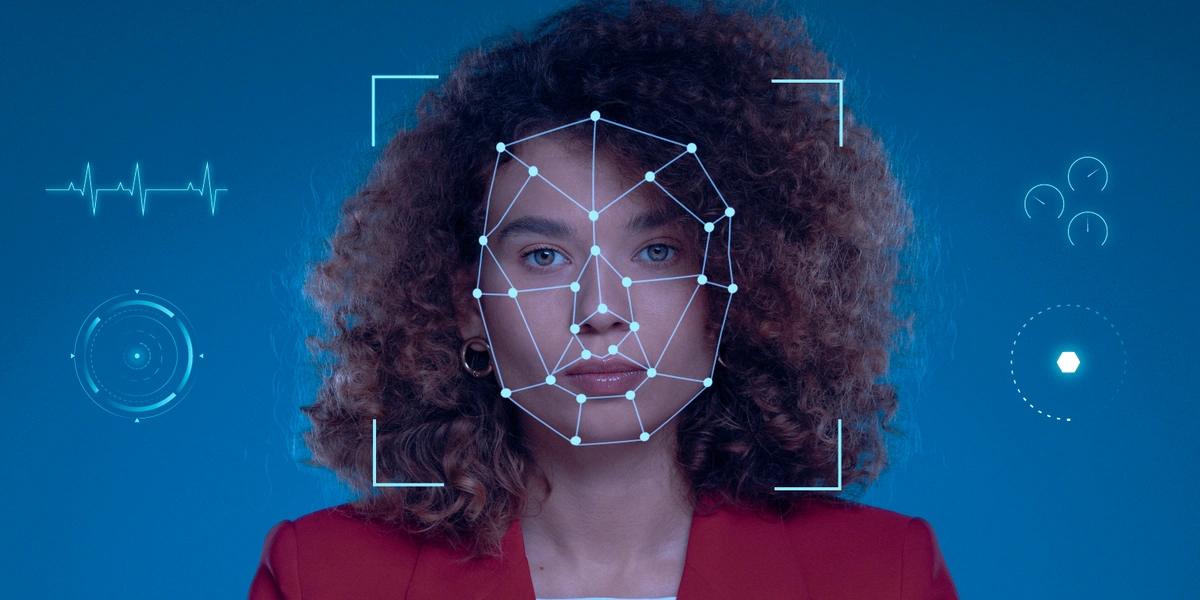
Authentication: This is the process of verifying the identity of a user, usually through the use of a username and password. Other methods of authentication can include biometric factors such as fingerprint, facial recognition, or a security token.
-
Authorization: Once a user has been authenticated, the IAM system determines what resources the user is authorized to access based on their job function, role, or other criteria.
-
Access management: Identity Access Management systems manage access to resources by enforcing access policies. Access policies define what resources users can access and what actions they can perform on those resources.
-
Identity governance: IAM systems also provide a way to manage user identities and their associated access rights over time. This includes creating and deactivating user accounts, assigning roles and permissions, and monitoring user activity for compliance and security purposes.
-
Single sign-on (SSO): IAM systems can provide a seamless sign-on experience for users by allowing them to access multiple applications and resources with a single set of credentials.
Overall, IAM systems provide a centralized way to manage digital identities and access to resources, helping organizations maintain security, compliance, and efficiency of functioning.
SecurePass IAM: eMudhra’s Comprehensive Identity and Access Management Solution
Benefits of Identity and Access Management (IAM)
With the digitization of workflows at organizational and governmental levels, the need of safeguarding corporate resources cannot be denied. As a result, manually assigning and tracking user privileges is not only tiresome but is error-prone and inefficient. Automating these tasks with IAM can help streamline the workflows and control granular access to all corporate assets.
The complete potential of IAM far exceeds the simple authentication of users. Biometrics, behaviour analytics, and AI are a few features to list. The rigorous control of IAM in highly dispersed and dynamic environments line up with the security requirement in the IoT ecosystem as well as with the large-scale shift from firewalls to a zero-trust model in enterprises.
Mentioned below are a few benefits of implementing Identity And Access Management in the cyber security of your digital ecosystem.
-
Improved security: IAM ensures that only authorized users can access sensitive resources, reducing the risk of data breaches and unauthorized access.
-
Increased compliance: It helps organizations comply with regulatory requirements such as HIPAA, GDPR, and PCI-DSS, by ensuring that access to sensitive data is restricted to authorized individuals.
-
Simplified access management: It enables organizations to manage access to multiple resources through a single system, reducing the complexity of managing access rights.
-
Improved user experience: IAM can improve the user experience by providing users with a single sign-on (SSO) capability, reducing the need for multiple passwords and login procedures.
-
Cost-effective: IAM can reduce the cost of managing access rights by automating access management processes and reducing manual effort and errors.
-
Better visibility and control: IAM enables organizations to monitor and track user access to resources, providing greater visibility and control over user activities.
Types of Digital Authentication Used in Identity and Access Management
While the IAM solution imbibes trust in the digital ecosystem of corporates and enterprises, industry leaders are now starting to realize the importance of implementing state-of-the-art cyber threat response strategies, including authentication as part of the process. The list below reviews some standard authentication methods used to secure modern systems.
-
Password-based authentication: This is the most common form of authentication, where users enter a username and password to access a system or application. It is vulnerable to hacking, phishing, and other attacks that compromise passwords.
-
Multi-factor authentication (MFA): This method adds multiple layers of security to password-based authentication by requiring a second form of authentication, such as a fingerprint scan, one-time password, or smart card.
-
Biometric authentication: This method uses physical characteristics such as fingerprints, facial recognition, or iris scans to verify a user's identity.
-
Certificate-based authentication: It utilizes digital certificates issued by a trusted third-party certificate authority (CA) to verify a user's identity. The certificate contains the digital identity of a user including a public key, and the digital signature of a certification authority. It can only be issued by a CA.
-
Token-based authentication: This method uses a physical device, such as a security token or smart card, to generate a unique code that is used to authenticate a user. Use cases of token-based authentication include RESTful APIs that are used by multiple frameworks and clients.
Identity and Access Management Solutions Suite: SecurePass IAM Demo Video Guide
How eMudhra can your Organization with Identity and Access Management Solutions?
Identity and Access Management solutions are transforming the way businesses operate for good. IAM implementation enables businesses to work more securely and productively, from granular access control to authentication and resource management, a comprehensive IAM platform is the solution.
Imbibe trust in your digital ecosystem with eMudhra’s future-ready Identity and Access Management solutions (SecurePass) which ensure trust, security, and global compliance. SecurePass is deployed widely across the private and public sectors to help kick-start your digital transformation journey. We offer access management powered by behavioral analytics, 15+ modes of authentication, Single Sign On, and adaptive authentication.
Contact us now to learn how SecurePass can help you achieve cybersecurity compliance and access governance.
